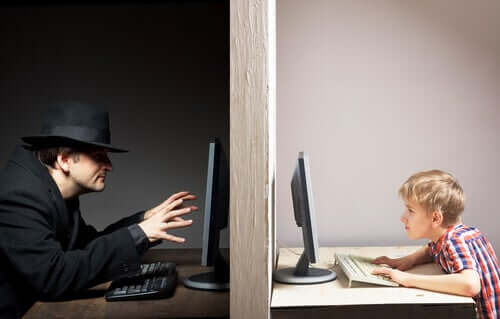
5 Internet Security Risks for Children and Teens

The many different Internet security risks that exist are very different from each other. Young people are more vulnerable to these risks. Keep reading to discover five Internet security risks for children and teens.
Internet security risks for children and teens
1. Cyberbullying
Unfortunately, cyberbullying is one of the most common security risks that children and teens may experience on the Internet. The aggressors usually take advantage of the protection and anonymity screens provide. In addition, cyberbullies were the ones that had the least consequences so far.
Also, cyberbullying not only takes place on social media, the most common places but also in online games. In these games, players risk being subjected to relentless attacks, which turn what could be a great virtual experience into a real nightmare.
2. Sexting
In itself, sexting, or sending sexually explicit images, videos, text messages, or emails, isn’t an Internet risk but rather a risky practice. For this reason, it’s essential to make young people aware of its possible consequences.
On many occasions, when parents want to prohibit children from doing something in particular, they get the opposite effect, especially with teens. Therefore, instead of scolding or lecturing your children, it’s much more effective to offer your children advice and information.
- Explain that there’s no 100% safe application to send photos. Thus, once they send any photo or video, it’ll be out of their control.
- Tell them not to store private photos on their devices, as they may not be well-protected. This means they run the risk of someone else posting them.
- Teach them that they can report these acts and that, if they share, forward, and comment on this type of content, they’ll not only be harming someone but will also be committing a crime.
3. Accidental download of malware
Malware is defined as unwanted malicious software that can install itself on devices, causing them to malfunction. This type of Internet security risk is quite common in teens. This is because many try to download movies, TV series, and games from a website with malware.
This is really dangerous because, once the system has been infected, there’s a possibility that a malicious attacker can access the computer. Antiviruses are essential to protect your children’s computer from possible malware. However, you also need to talk to them and teach them to be careful on the Internet.
4. Phishing
Phishing is a technique that consists of using emails to scam and fraud. With just a click on a link, you run the risk of automatically downloading malicious attachments or of being redirected to a fraudulent web page in order for you to log in to some web application: banking, social media, etc.

These malicious messages and emails can appear at any time, as the people who commit this type of crime know the most popular web pages among young people.
For this reason, it’s important to teach children and teens to distrust these types of messages and know how to detect them. How to detect a phishing email? Possible clues include: If the email asks you to log into a social media network, if it’s written in another language, if the sender is strange, or if the email is poorly written.
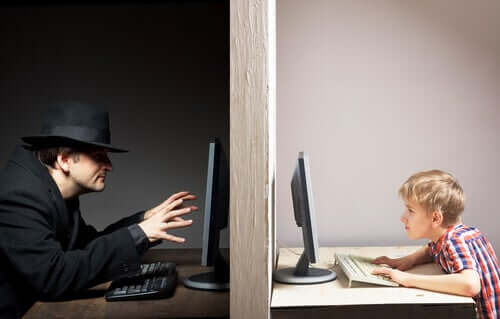
5. Sharing private information is one of the biggest Internet security risks for children and teens
Nowadays, young people constantly communicate through social media networks and post photos and videos on them. If they aren’t careful, it’s likely that their personal information will be accidentally displayed online. For example, their home address, mobile phone numbers, or location.
Children and teens don’t pay much attention to this, as they aren’t aware of the possible risks that this may have. Thus, you should have a conversation with them about the possible consequences of not being careful when they post on social media networks.
In short, to fight these risks, you must know about them and how to detect them, raising awareness of their possible consequences with your children and teens.
The many different Internet security risks that exist are very different from each other. Young people are more vulnerable to these risks. Keep reading to discover five Internet security risks for children and teens.
Internet security risks for children and teens
1. Cyberbullying
Unfortunately, cyberbullying is one of the most common security risks that children and teens may experience on the Internet. The aggressors usually take advantage of the protection and anonymity screens provide. In addition, cyberbullies were the ones that had the least consequences so far.
Also, cyberbullying not only takes place on social media, the most common places but also in online games. In these games, players risk being subjected to relentless attacks, which turn what could be a great virtual experience into a real nightmare.
2. Sexting
In itself, sexting, or sending sexually explicit images, videos, text messages, or emails, isn’t an Internet risk but rather a risky practice. For this reason, it’s essential to make young people aware of its possible consequences.
On many occasions, when parents want to prohibit children from doing something in particular, they get the opposite effect, especially with teens. Therefore, instead of scolding or lecturing your children, it’s much more effective to offer your children advice and information.
- Explain that there’s no 100% safe application to send photos. Thus, once they send any photo or video, it’ll be out of their control.
- Tell them not to store private photos on their devices, as they may not be well-protected. This means they run the risk of someone else posting them.
- Teach them that they can report these acts and that, if they share, forward, and comment on this type of content, they’ll not only be harming someone but will also be committing a crime.
3. Accidental download of malware
Malware is defined as unwanted malicious software that can install itself on devices, causing them to malfunction. This type of Internet security risk is quite common in teens. This is because many try to download movies, TV series, and games from a website with malware.
This is really dangerous because, once the system has been infected, there’s a possibility that a malicious attacker can access the computer. Antiviruses are essential to protect your children’s computer from possible malware. However, you also need to talk to them and teach them to be careful on the Internet.
4. Phishing
Phishing is a technique that consists of using emails to scam and fraud. With just a click on a link, you run the risk of automatically downloading malicious attachments or of being redirected to a fraudulent web page in order for you to log in to some web application: banking, social media, etc.

These malicious messages and emails can appear at any time, as the people who commit this type of crime know the most popular web pages among young people.
For this reason, it’s important to teach children and teens to distrust these types of messages and know how to detect them. How to detect a phishing email? Possible clues include: If the email asks you to log into a social media network, if it’s written in another language, if the sender is strange, or if the email is poorly written.
5. Sharing private information is one of the biggest Internet security risks for children and teens
Nowadays, young people constantly communicate through social media networks and post photos and videos on them. If they aren’t careful, it’s likely that their personal information will be accidentally displayed online. For example, their home address, mobile phone numbers, or location.
Children and teens don’t pay much attention to this, as they aren’t aware of the possible risks that this may have. Thus, you should have a conversation with them about the possible consequences of not being careful when they post on social media networks.
In short, to fight these risks, you must know about them and how to detect them, raising awareness of their possible consequences with your children and teens.
All cited sources were thoroughly reviewed by our team to ensure their quality, reliability, currency, and validity. The bibliography of this article was considered reliable and of academic or scientific accuracy.
- Swimmer, M.G. (2005). Malware Intrusion Detection. Lulu. Recuperado de
- CCN-CERT (2019). Phising. Recuperado de: https://www.ccn-cert.cni.es/component/tags/tag/phishing.html
This text is provided for informational purposes only and does not replace consultation with a professional. If in doubt, consult your specialist.








